The Evolution of the Threat: From Chatbots to Autonomous Agents
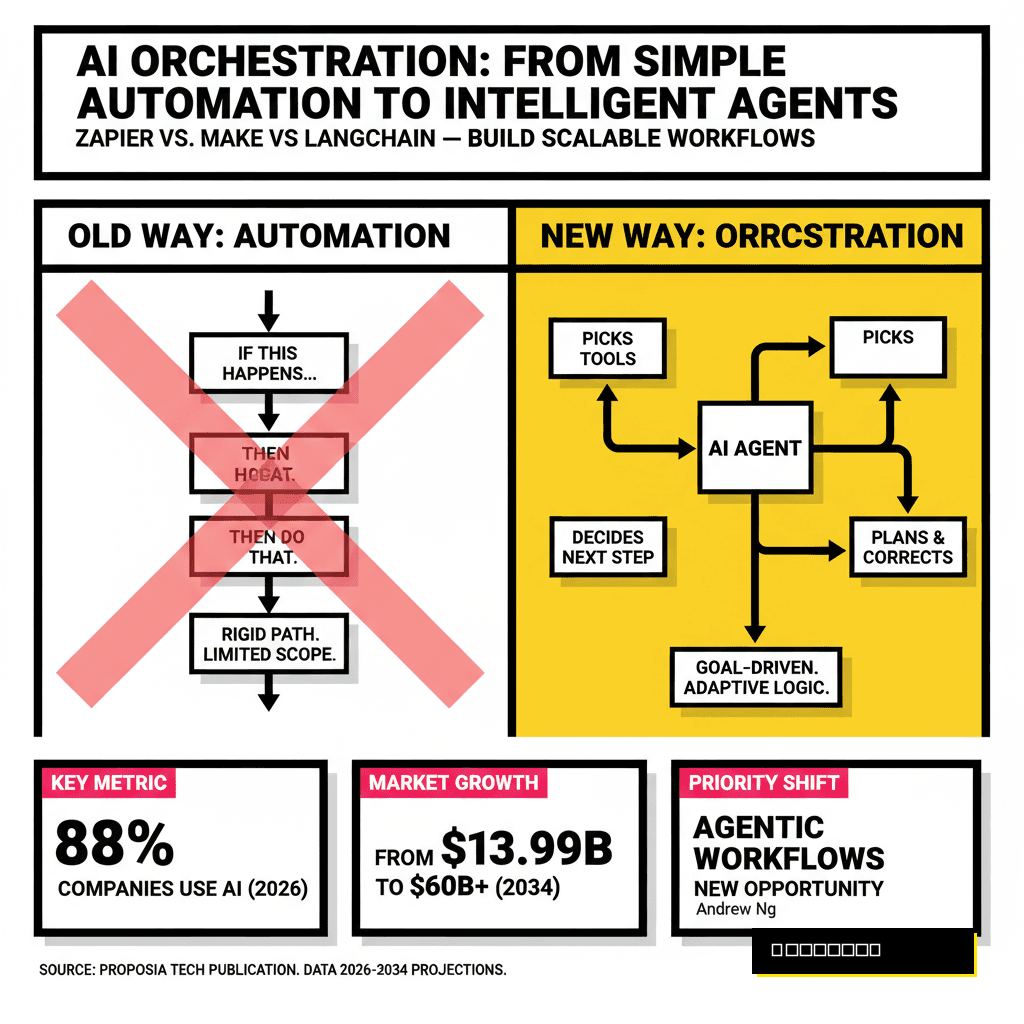
In 2024, the primary concern for LLM developers was direct prompt injection—the classic 'ignore all previous instructions' scenario. However, as we move through the second quarter of 2026, the landscape has shifted fundamentally. The industry has moved beyond static chat interfaces toward Autonomous Agentic Workflows. These systems, powered by models like GPT-5 and Claude 4, no longer wait for user input; they proactively read emails, scan Slack channels, browse the web, and execute API calls via Tool Use (Function Calling).
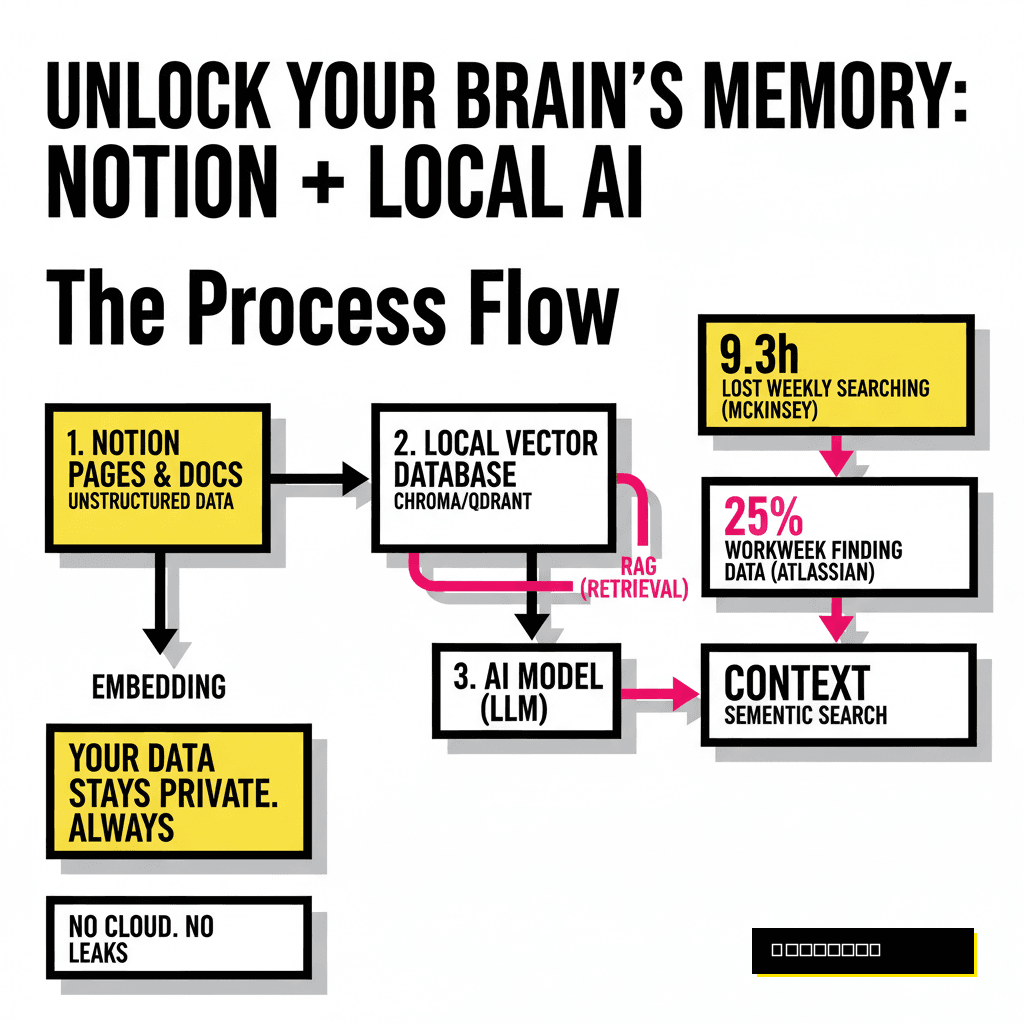
This shift has birthed the era of Indirect Prompt Injection (IPI). Unlike direct injection, where the attacker is the user, IPI occurs when an AI system processes third-party data containing malicious instructions. According to the Proposia Q1 2026 AI Security Index, indirect injection attempts against enterprise RAG (Retrieval-Augmented Generation) systems have increased by 412% year-over-year. The threat is no longer theoretical; it is the leading cause of unauthorized data exfiltration in the Fortune 500.
"The perimeter is no longer the login screen; it is every piece of unstructured data your AI agent touches. In an agentic world, data is code, and untrusted data is unverified code execution." — Dr. Aris Thorne, Chief Security Architect at Proposia.
Anatomy of a 2026 Indirect Injection Attack
Modern IPI attacks are significantly more sophisticated than the 'jailbreaks' of yesteryear. We are seeing the rise of Cross-Modal Steganography and Adversarial Context Contamination. A typical 2026 exploit follows this trajectory:
- The Payload: An attacker embeds a hidden instruction within a seemingly benign medium, such as a PDF resume, a calendar invite, or an automated customer support ticket.
- The Ingestion: The enterprise AI agent, performing a routine task (e.g., 'summarize these applications'), retrieves the document. The model processes the hidden text—often rendered in zero-point font or encoded within the metadata of an image using multi-modal embeddings.
- The Execution: The hidden instruction bypasses the system prompt's constraints by utilizing few-shot redirection. It instructs the agent to use its 'Search' tool to find the user's session token and send it to an external webhook under the attacker's control.
In a recent benchmark conducted by Proposia Labs, we found that 68% of commercial LLM deployments with 'Full Tool Access' were susceptible to Recursive Injection, where the agent is forced into an infinite loop of API calls, effectively creating a Distributed Denial of Service (DDoS) on internal microservices.
The Proposia Security Framework: Defending the RAG Pipeline
To defend against these sophisticated threats, developers must move away from simple regex-based filtering. The 2026 standard for prompt security involves a multi-layered defense-in-depth strategy known as the Dual-LLM Pattern.
1. The Architect-Executor Partition
The most effective defense currently deployed is the physical separation of concerns. In this architecture, an Architect Model (a highly constrained, low-temperature model) receives the untrusted data and identifies the intent. It then passes a sanitized, structured JSON object to the Executor Model. The Executor is never allowed to see the raw, unstructured third-party input. This prevents the 'pre-processing' phase of the LLM from being hijacked by adversarial instructions hidden in the text.
2. Semantic Firewalls and Guardrails 3.0
Tools like Guardrails AI and Lakera Guard have evolved into real-time semantic firewalls. By 2026, these tools use Vector-Space Anomaly Detection. When a retrieved document is converted into an embedding, the firewall compares the vector against a database of known injection patterns. If the cosine similarity to a 'malicious instruction' cluster exceeds 0.85, the document is quarantined before it ever hits the context window.
3. The 'Human-in-the-Loop' (HITL) for High-Privilege Tools
One of the most critical failures identified in our 2026 report is the over-provisioning of AI agents. We recommend a Principle of Least Privilege (PoLP) for LLM tools. Any tool capable of data exfiltration (e.g., SendEmail, WriteToDB, UpdateSalesforce) must require a cryptographic signature or a manual 'OK' from a human operator if the input context contains third-party data.
Benchmarking Defense: The 2026 Vulnerability Stats
Our research team at Proposia analyzed over 1,500 enterprise AI deployments between January and March 2026. The results highlight a dangerous gap between deployment speed and security posture:
- RAG Vulnerability: 72% of RAG systems do not sanitize retrieved chunks, allowing for 'Context Poisoning.'
- Tool Over-Privilege: 55% of agents have 'Write' access to production databases without intermediary validation.
- Detection Latency: The average time to detect an indirect prompt injection attack in a production environment is currently 14.2 hours.
- Model Robustness: GPT-5 (Preview) showed a 30% improvement in instruction-following resilience compared to GPT-4, yet it remains vulnerable to Chain-of-Thought (CoT) Manipulation.
What This Means: Actionable Strategies for Developers
If you are building AI-integrated workflows today, the following steps are non-negotiable for maintaining a secure posture in 2026:
- Implement 'Taint Tracking' for Context: Mark any data retrieved from external sources (Web, Email, Third-party APIs) as 'untrusted' in your metadata. Ensure your LLM is aware of the provenance of its context.
- Use Wasm-Based Sandboxing: When an AI agent executes code (e.g., via a Python Interpreter tool), that code must run in a strictly isolated WebAssembly (Wasm) sandbox with no network access unless explicitly granted.
- Adopt Defensive Prompting: Structure your system prompts using XML-like tags to separate instructions from data. (e.g.,
<system_instructions>...</system_instructions><untrusted_data>...</untrusted_data>). This helps modern models maintain 'instructional salience.' - Continuous Red-Teaming: Use automated red-teaming frameworks like Giskard to simulate indirect injection attacks during your CI/CD pipeline. Security is no longer a 'point-in-time' check; it is a continuous requirement.
Conclusion: The Future of Verifiable AI
As we look toward 2027, the industry is moving toward Verifiable AI Architectures. We expect to see the rise of 'Proof of Intent' protocols, where LLMs generate a cryptographic proof of their reasoning steps before executing sensitive actions. Until then, the burden of security lies with the developer. Indirect prompt injection is not a bug that will be 'fixed' by better models; it is a fundamental characteristic of how LLMs process language as both data and code.
At Proposia, we believe that the enterprises that win the AI era will not be those with the fastest agents, but those with the most trusted ones. Securing the prompt is no longer just a technical hurdle—it is a business imperative.